Recalling RFID: Full Report
 Recalling RFID was held on Friday the 19th and Saturday the 20th of October at de Balie. This unique event included presentations on RFID, debates and digital connectivity scenarios by industry representatives, academics, artists, privacy advocates, programmers and consultants. Recalling the current state of affairs and looking to the future, it turned out to be a very interesting, high quality conference.
Recalling RFID was held on Friday the 19th and Saturday the 20th of October at de Balie. This unique event included presentations on RFID, debates and digital connectivity scenarios by industry representatives, academics, artists, privacy advocates, programmers and consultants. Recalling the current state of affairs and looking to the future, it turned out to be a very interesting, high quality conference.
Speakers included Katherine Albrecht (CASPIAN – Consumers Against Supermarket Privacy Invasion And Numbering, USA), Bart Schermer (privacy lawyer and coordinator of RFID Platform Netherlands), Rafi Haladjian (founder of Violet company – known from the Nabaztag Rabbit, tech entrepreneur), Melanie Rieback (Ubisec researcher who invented the first RFID virus, VU University Amsterdam), Stephan Engberg (Priway/Copenhagen Business School), Christian van ‘t Hof (researcher, Rathenau Instituut), Willem Velthoven (designer and director of Mediamatic), interaction designer Timo Arnall, and many others.
This summary and review assumes that readers have at least a vague notion of what Radio Frequency Identification (RFID) is. But just to recall:
RFID makes it possible to identify and track just about any physical object you can think off – books, car tires, shoes, medicine bottles, clothing, pets, and even human beings.
The “RF” part of RFID stands for “radio frequency” and explains how RFID does its tracking: It uses electromagnetic energy in the form of radio waves to communicate information at a distance.
— Katherine Albrecht, Spychips, 2005
RFID and Police Investigation
 Christian van ‘t Hof gave the first presentation on ‘RFID and police investigation’. He began by asking how many people had RFID on them at the moment, and the vast majority of the audience raised their hand immediately. He used this to assess the level of knowledge in the audience: most people in the Netherlands do not realize that, on average, they carry around three RFID tags everyday. Christian works for the Rathenau institute, a think tank that investigates new technologies and advises the Dutch parliament. His presentation thus concerned the public support of RFID and the related political debates and legal questions.
Christian van ‘t Hof gave the first presentation on ‘RFID and police investigation’. He began by asking how many people had RFID on them at the moment, and the vast majority of the audience raised their hand immediately. He used this to assess the level of knowledge in the audience: most people in the Netherlands do not realize that, on average, they carry around three RFID tags everyday. Christian works for the Rathenau institute, a think tank that investigates new technologies and advises the Dutch parliament. His presentation thus concerned the public support of RFID and the related political debates and legal questions.
So what is the use of RFID for government? With RFID becoming a part of everyday life, it is digitalizing public space. Knowing the ID of an RFID means knowing a time, a place, and an action. In the Netherlands this is most clearly seen in public transport (a system now being implemented uses RFID for ticketing), and in new passports (where not only RFID is integrated but also some biometric data). RFID used in this way means that you leave digital traces in public space. So how, for instance, might RFID be used for police investigation? Van’t Hof takes us through a scenario involving the new transportation system.
When you have a personal travel card for public transport, the identity of the chip is connected to your personal data (and it is worth noting that such subscriptions are cheaper than anonymous tickets). Because the system knows who was where at what time, this data can be used for criminal investigation. Van’t Hof says this is a clear-cut benefit in some cases: say, when a murder that takes place in the subway, it will give police easy access to witnesses and possible suspects. But things get trickier when it goes a step further. For instance, through profiling it may also be possible to find out who is evading taxes. The person who collects unemployment benefits but is always in transit during rush hours may be flagged as a possible offender. Such profiling could also be used to find potential terrorists, but here one already runs into the problem of effectiveness versus potential misuse.
In every new Dutch passport there is some biometric data (your passport photo and, by 2009, your fingerprints). The picture on this passport needs to be taken in a specific manner: your face must match ‘the matrix’ (seriously, this is the technical term). Currently, the ORRA system (Online Raadpleegbare Reisdocumenten Administratie) is being proposed for storing personal and biometric data in a central database, with the justification that it will prevent passport fraud. But this database also provides a valuable resource for authorities as it can be used to profile, investigate and research.
Van’t Hof also discussed research into the public perception of RFID. When doing focus group research, the Rathenau institute expected to find that people would not know a lot about RFID and would be offended by the possibilities of its misuse. As much of the available information on RFID relates to technical issues, it was no surprise that their first intuition was correct. Less expected, however, was what focus groups said about RFID after hearing details on what it is:
- Many in the focus groups said it was only ‘natural’ for such information to be collected in a central database used by the government.
- When asked if travel data should be linked to a specific person, 72% said this was okay for finding suspects of a crime, 61% went a step further and agreed that witnesses of a crime should be found, and a startling 60% said that public transport should be fully personalized – meaning that the transport companies and the government would always know who was where doing what.
- When asked about using biometric data from passports, 55% said the photos could be used for investigations, 65% said the fingerprints could be used for investigation, 52% said it could be used for international data exchange, and 62% said it could be used to identify a person via security camera.
Christian van ‘t Hof did note that “public opinion can be slippery” and that perhaps the public first needs to fully understand what RFID is and how it can be used. Furthermore, the context of the questions – criminal investigation – might as well have influenced the results. Further research with questions related to RFID in different contexts is therefore needed to get more solid results regarding public perception of RFID. The public opinion reflected in these results did however lead him to prediction that we will go to fully personalized transport (as we have with airplanes) and that it will be used to track and investigate. What he did not touch on, however, is that there is a great difference between airlines and subways – public transport is something one has a right to, so the analogy with air transport is questionable.
Rathenau takes the RFID debate beyond privacy issues by taking into consideration the costs involved in getting this system to work effectively for criminal investigation. For the system to work, all parties involved should store personal data in a standardized way limiting errors and incomplete databases. Telephone and Internet providers already store and make available telecommunication data for a period of six moths for police investigation under Centraal Informatiepunt Onderzoek Telecommunicatie (CIOT). This law implemented by government brought with it enormous costs and efforts for providers. Implementing similar laws for the public transport system will also increase costs which will eventually be payed by the public.Researching public perception of RFID in the context of costs involved will probably lead to different results than in the criminal investigation context. Christian tells us that the RFID issue is currently only considered by the ministry for economic affairs, and that this is one of the major obstacles in taking up RFID in a responsible way. His message to the parliament is fivefold:
- have a clear position on centralizing biometric data,
- have a clear position on using travel data,
- do more research on effectiveness,
- question if there should be data retention laws for RFID or not,
- explain your vision on RFID, privacy, innovation, and investigation.
The question of effectiveness would be posed a couple of times today. The most famous example is that although the police knew, or at least had information on, the Hofstad network and their planned attacks, they were unable to act on it. Will more surveillance data lead to a safer society?
For more information on ORRA and the statistics mentioned, see this Dutch paper of the Rhatenau institute.
RFID guardian
VU researcher Melanie Rieback is known worldwide for her expertise on RFID and privacy, but especially for her implementation of the first RFID virus.  Melanie started off with some history about RFID. As far back as World War II RFID was used in planes to identify themselves as being ‘friend or foe’ or, more accurately, ‘identify or die’. The system was ad hoc, as pilots would adjust their altitude or trajectory in a way that radar operators would understand. As such, the system suffered from ‘Denial Of Service’ attacks and a lot of ‘friends’ ended up being shot as well. From the start, then, Rieback argues that trust in a system is crucial. Later on RFID was used as a binary system against theft in clothing stores (remember the big white buttons). Such systems were easily fooled by using, for example, a bag with an inner-casing made of aluminum so that the chip could not be read. Over the last few years RFID has further been developed to contain 96 bits (enough to uniquely number every item produced on earth for the next thousand years). It is now mainly deployed under the banner of improved logistics.
Melanie started off with some history about RFID. As far back as World War II RFID was used in planes to identify themselves as being ‘friend or foe’ or, more accurately, ‘identify or die’. The system was ad hoc, as pilots would adjust their altitude or trajectory in a way that radar operators would understand. As such, the system suffered from ‘Denial Of Service’ attacks and a lot of ‘friends’ ended up being shot as well. From the start, then, Rieback argues that trust in a system is crucial. Later on RFID was used as a binary system against theft in clothing stores (remember the big white buttons). Such systems were easily fooled by using, for example, a bag with an inner-casing made of aluminum so that the chip could not be read. Over the last few years RFID has further been developed to contain 96 bits (enough to uniquely number every item produced on earth for the next thousand years). It is now mainly deployed under the banner of improved logistics.
Melanie is concerned with the fact that most tags do not use any privacy or security protection measures. Most RFID tags happily yell their ID to every reader in the neighborhood. In this way the tags ‘leak’ a lot of information, which is something RFID readers are guilty of too.
To improve RFID, Rieback says, we need to start thinking of it as computing. Tags are low-end computers, yes, but computers all the same. After the mainframe, minicomputers, PCs and embedded computers, there is RFID: the smallest computing unit today. If you want to build the so-called “Internet of Things”, all of the problems with the internet now will also affect the new technology. Melanie’s point is that right now users of RFID have no control whatsoever about who or what reads which tags when. Therefore she is currently developing the RFID guardian.
The RFID guardian is focused on putting security and privacy into RFID. The three main goals are to investigate the security and privacy threats faced by RFID systems, to design and implement real solutions against these threats, and to investigate the associated technological and legal issues. The RFID guardian would act as a kind of radio-frequency firewall, one that could be housed in mobile phones. The main characteristics of the device should be that it is portable, battery powered as well as provide and secure two-way RFID communication. It must act like an RFID reader, but also as an RFID tagger. It will have to imitate, spoof and simulate multiple RFID tags.
Touching on why such security is so important, Melanie points out that the new chip system for public transport was easily hacked. A group of UvA Master students hacked one of the cards within a week. Knowing how expensive this system was, this is worrying: perhaps companies behind RFID do not know where to go with their security questions?
After her presentation, Rieback was asked about the legitimacy of such a project: couldn’t it be used to attack systems? Her response was that it could of course be used maliciously as well but that turning your back on the current threats was not the solution either.
Melanie Rieback showing the RFID guardian:
The RFID guardian will be relaunched on the first of November with a completely refashioned website, wiki, forum, blog and open-source schematics. Be sure to check rfidguardian.org!
Interaction Space
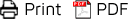
Timo Arnall talked about RFID in Interaction Design. We have currently entered a phase of social and tangible computing where the focus is much more on human capabilities. The current discourse about RFID is clouded by metaphors because it does not have a single shape. Arnall calls for increased visibility of RFID in design, so as to show the different shapes and forms that RFID comes in. Every medium has its own voice, and with the right designs different RFID readers and cards would become different expressions. Such a visual language is formed culturally – in Japan for example, RFID has a very friendly face:
RFID is in need of some demystification, as it is notoriously ‘invisible’. Designers must be creative and find ways to manage RFID’s visibility. While the technique is usually hidden, the experience of it does not have to be. How can we visualize what goes on behind the tag, in the network? What are the actions that are being triggered in the network when you swipe an RFID tag? How can we visualize different uses and actions of RFID?
With his presentation, Arnall showed us that RFID is not only a security risk but also a space opening up for internal action, one that designers can and will visualize, design and potentially manage.
The Library and Social Networks
 Willem Velthoven heads Mediamatic, and began by presenting some RFID projects the company and foundation has been involved in. The first of these was the symbolic table. This ‘interface free” table allowed users to simply tag objects and to play with (Web) content in a tactile way. Other projects were those displayed at the PICNIC conference, such as the ‘friend finder’. This application allows conference visitors to meet up in real space and become friends on an online social network at the same time. Using RFID tokens they print out business-cards with their profiles on them. As an added incentive, they can get a free beer. So, in essence, the installation uses and manipulates digital data through physical interaction.
Willem Velthoven heads Mediamatic, and began by presenting some RFID projects the company and foundation has been involved in. The first of these was the symbolic table. This ‘interface free” table allowed users to simply tag objects and to play with (Web) content in a tactile way. Other projects were those displayed at the PICNIC conference, such as the ‘friend finder’. This application allows conference visitors to meet up in real space and become friends on an online social network at the same time. Using RFID tokens they print out business-cards with their profiles on them. As an added incentive, they can get a free beer. So, in essence, the installation uses and manipulates digital data through physical interaction.
Another PICNIC project was iTea, which was also a conversation starter. By placing one’s tag in the teacup, visitors would receive personalized data taken from both their personal profiles as well as from a Google query of their name. This gave the users an impression of the possibilities of data mining, profiling and RFID. The Photo Booth was also very popular at PICNIC, and allowed people to get their picture taken with friends and interact with one another using RFID.
The latest Mediamatic project involves the new public library of Amsterdam. Where libraries increasingly face the challenge of ‘upgrading’ to current information and searching demands, there is also a possibility for innovation.
Velthoven was asked to reflect on the whole process of lending- and returning books, in this case by use of RFID and/or ‘traditional’ bar-codes. Although the project and implementation is just beginning, some critical questions and remarks were already clear. For instance, he noted a security concern, since it easy to gain access to others’ data. But this data could also be used differently: if a digital system for accessing lending data is already in place, why not make it possible to share that data?
The main question for the project concerns the (changing) role of a library today. Velthoven suggested that, through new technologies and social networking sites like the ones used at PICNIC, the library could become a social meeting place, where instead of reading in silence, one could meet up with fellow-readers, have book discussions, share interests etc. What Velthoven did not address is whether this should be the primary aim of a library, or whether or not there are already non-technical ways of achieving the same goals (e.g. book clubs).
Velthoven concluded with a simple message, ‘Make it fun again!’ Using online social networks in combination with new technologies like RFID, he sees a different path for classic institutions like the library.
RFID in japan – Ubiquitous Network Society
 Wouter Schilpzand is a researcher at the Technical University of Eindhoven. He conducted a couple of months of field-research into location-based services in Japan. With an overload of examples, from the Oyster-card and a number of mobile-phone applications for (among other things) public transport payments, the message was that the integration of technology in Japan is way ahead of Europe. The question why, however, was not really addressed, though, which is a pity. By only looking at the results of this techno-saturation, Schilpzand’s presentation missed an opportunity.
Wouter Schilpzand is a researcher at the Technical University of Eindhoven. He conducted a couple of months of field-research into location-based services in Japan. With an overload of examples, from the Oyster-card and a number of mobile-phone applications for (among other things) public transport payments, the message was that the integration of technology in Japan is way ahead of Europe. The question why, however, was not really addressed, though, which is a pity. By only looking at the results of this techno-saturation, Schilpzand’s presentation missed an opportunity.
That Japanese culture is a mix of tradition and technology is well known, so the story about how gadget-friendly the early adopters are could be expected. One outcome of ‘successful’ dissemination is that the average Japanese consumer is less critical and more open to new applications and new technologies. Where the European market is interested in established products and known for watchdog-like skepticism, the Japanese prosumer is more willing to give feedback and thus contribute to the research and development of new commercial technologies.
The conclusion of his talk was that we should look more at the rapid development of Japanese RFID and mobile technology. What he did not point out is that this cannot be reproduced directly elsewhere, since there are cultural differences and problems of scale and infrastructure (Japan is a relatively secluded area and the population is concentrated in big cities with a strong, cohesive culture).
Perhaps the rise of what Bruce Sterling calls the Spime or technology Wrangler will teach us to be less afraid of upcoming technologies, and possibly without losing skepticism. That Schilpzand’s presentation was so different to the rest serves as a reminder that Anglo-American fears of big brother-scenarios still rule discussions of RFID technology. Highlighting the divide, he argued that the dangers of RFID mentioned by Rieback and others, while very interesting, are a repetition of warnings, rather than proposals for solutions.
Serious Gaming
Rafi Haladijan is one of the founders of a Paris-based company called Violet, which recently gained international fame with its product, the Nabaztag. This is (in our view) the first real consumer product that deals with widely discussed phrases like Ambient Intelligence and the internet of things. Before going into more detail on the product, Haladijan gave the audience some background information.
Violet was founded in 2003, when the internet was viewed somewhat differently; with unstable connections, low connectivity and slower modems, the goal of ‘developing infrastructure and services to link all types of objects’ was far-fetched. Nonetheless, Violet looked to move in this direction by focusing on the meaning of phrases like calm technology and ubiquitous computing.
The first instance of inspiration he mentioned is the talking teddy bear. Mixing views on Moore’s law and evolution, Haladjian explains that the teddy bear carries the statement that everything will indeed be hooked up to some kind of network via some sort of electronics. Not because of a technological drive being imposed on society, but simply an inevitable evolutionary step.
 According to Haladijan, the reason why big players like Philips and Sony have not entered the market of home-entertainment / ambient intelligence yet is due to their approach. These companies focus on creating a ‘smart-home’, but do so with a naive vision on user-technology interaction. The smart home is one very expensive product with no real killer application, and thus exactly misses the point. In a time where we are halfway between the Flinstones and the Jetsons, the question is how to shape the road we are on now. We all have to do this, he says, and not leave it to bulky tech-companies. This is why Violet aims to create affordable products (20 to 200 euro) within the realm of Ambient Intelligence, with a focus on poetic and fun applications. Haladijan reasons that, by creating affordable products, people will understand the new technologies better and be able to create their own needs and values on that basis. By empowering people to do certain things with their products, a more diverse and more interesting adoption of technology will emerge naturally. What he proposes, then, is a bottom-up approach to consumer adoption of RFID.
According to Haladijan, the reason why big players like Philips and Sony have not entered the market of home-entertainment / ambient intelligence yet is due to their approach. These companies focus on creating a ‘smart-home’, but do so with a naive vision on user-technology interaction. The smart home is one very expensive product with no real killer application, and thus exactly misses the point. In a time where we are halfway between the Flinstones and the Jetsons, the question is how to shape the road we are on now. We all have to do this, he says, and not leave it to bulky tech-companies. This is why Violet aims to create affordable products (20 to 200 euro) within the realm of Ambient Intelligence, with a focus on poetic and fun applications. Haladijan reasons that, by creating affordable products, people will understand the new technologies better and be able to create their own needs and values on that basis. By empowering people to do certain things with their products, a more diverse and more interesting adoption of technology will emerge naturally. What he proposes, then, is a bottom-up approach to consumer adoption of RFID.
Within a standard Western home, a person owns approximately 6000 to 8000 objects, of which maybe five of them are linked to a network (radio, phone, television, computer). The aim is to link all 8000 objects to a network, talking to each other – exchanging information, ultimately linking everything in the world together!
For the Violet company the first step was a networked lamp, a strange precursor given that their prize product now is the NaBaztag, the world’s first smart rabbit. Using an anthropomorphic shape as an interface, the NaBaztag is a more attractive way to interact with a network. In other words, it creates a portal to an internet or network without a screen, but a connection that it is more intuitive than scree-based interfaces.
Next up is the Nazbaztag/tag, which is equipped with an RFID reader. The reason behind this is that it will integrate with Ztamps, tags which you can stick on almost anything. When the Ztamps comes near the rabbit (or the other way around), content can be triggered, anything from sound, lights, website to mail. The nice thing about this very simple but effective application is that one can contextualize and confine digital content to physical objects. Again here the philosophy is to not project a function onto the user, but to give user-generated content a chance with this technology in the belief that cool things will emerge through use. As a concluding statement, Haladjian reminds us that this all really comes down to storytelling and creating new and exciting ways to facilitate it (especially where interaction is the story!).
q&a
In the short q&a, which was more of a summary, the overall message was that we have to move interactions away from the screen and shift towards a new interaction paradigm. RFID should not be used as ‘another way to load stuff on your screen’, as Timo Arnall put it.
The great advantage to moving away from the screen is that we can move away from the world of metaphors (like the desktop metaphor on screen) to direct couplings of meaning and action. According to Haladjian, ‘We have to make a bridge from screen to the real world again, where the challenge is the spreading and representation of data.’
Spy Chips
 For a couple of years now, Katherine Albrecht has been on a crusade against RFID. She is well known for her book and website Spychips, and the revised version of that book written especially for Christians (where she recognized that RFID could be thought of as the biblical ‘mark of the beast’). Although some of us expected an extreme activist with little ‘content’, only the former was true. Albrecht was eloquent, and showed that she is very knowledgeable about RFID and its applications and uses.
For a couple of years now, Katherine Albrecht has been on a crusade against RFID. She is well known for her book and website Spychips, and the revised version of that book written especially for Christians (where she recognized that RFID could be thought of as the biblical ‘mark of the beast’). Although some of us expected an extreme activist with little ‘content’, only the former was true. Albrecht was eloquent, and showed that she is very knowledgeable about RFID and its applications and uses.
She began by noting that the RFID industry always draws an analogy with the barcode or UPC, saying RFID just makes things easier. However, she explains, there are three major differences that must be considered when an ID is connected with a database and remotely readable:
- Unique Codes – think about the same UPC on each bottle of coke versus a unique code on each bottle which allows cross-referencing (and again, creating knowledge of a time, a place, and an action),
- Involuntary – RFID is readable without you knowing it versus handing over an item to be scanned,
- Fields – RFID works with an electromagnetic field
 These points were elaborated upon in the rest of Albrecht’s talk. First of all she described the history of tracking items: from barcodes (for products) to loyalty cards (personal identifiers) to RFID (which allows for information on when, where and why consumers use products).
These points were elaborated upon in the rest of Albrecht’s talk. First of all she described the history of tracking items: from barcodes (for products) to loyalty cards (personal identifiers) to RFID (which allows for information on when, where and why consumers use products).
Albrecht told a couple of stories of the industry deploying RFID without letting the consumers know that they were being ‘spied’ upon. As an example you might want to look at the case of Gilette, the company that secretly took pictures of customers taking razor blades from the shelves. Apparently the industry does not want the public to know that they are using RFID and what it is used for, as Albrecht has been to various meetings where the industry was talking about strategies against consumer backlash.
Albrecht also explained the difference between a chip and a tag. A chip is a tag plus an antenna. Inkode now has a chipless tag, making RFID possible through the physical property of the tag itself – no electronics involved. With the advent of conductive ink, the packaging of an item can now become an antenna. This means that RFID can be truly invisible. And yet, no laws are in place to make sure consumers know when something is tagged with RFID. When products are tagged with RFID at the source (by the supplier), tags can be embedded deep into the object with little or no chance for removal.
Wall-Mart for example, now only works with suppliers who have RFID in their products. The company has also started item level tagging, despite the Code of Conduct they signed in accordance with CASPIAN and the privacy rights clearing house.
One result of this is that, in the near future, your trash will tell all kinds of secrets. Items will be tagged with RFID and a city may routinely scan your garbage, learning about the products you have bought and where you got them, or where you have been (you bought it in one place but threw it away somewhere else), and in that way be able to make specific profiles about you. This way your trash will be worth a lot of money! Even short-range RFID, then, can be very invasive.
Quoting from the report of Twan Eikelenboom at Viruteel Platform to give you the rest of Albrecht’s talk:
Implementation of the tag is all about hiding it: ‘You can sandwich RFID tags in shoes. And once this is done you can be identified everywhere: when you pass doorways, ceilings and floors you can be identified’. But what about RFID tags molded into tires? Or RFID tagged swipeless credit cards? The effects of implementation are still every unclear, as this article mentioned by Albrecht shows: Chip Implants Linked to Animal Tumors.
After implementation in everyday life, applications can be deployed. Some applications are already in use, for example in amusement parcs such as Alton Towers and LEGOland. You could say that this is merely in an amusement parc setting. IBM however has patented the Person Tracking Unit. This specific patent places RFID readers in the environment and as people walk around it tracks their movement and records products they carry with them. This could mean that “they” could look inside a woman’s bag to see, for example, if she carries babyfood and in turn use that for marketing purposes. Besides IBM, Bellsouth/Cingular has patented perhaps the most privacy invading example, which is about ‘post consumption information’ or simply put: garbage scanning.
The answer according to Albrecht lies in action. As an example she mentions the hidden RFID chips found at the Future Store in Germany. Metro Group had hidden RFID chips in loyalty cards and through protest, the company had to comply with privacy laws. More action is needed according to Albrecht to stop projects such as the forced chipping of Alzheimer patients.
At the recalling RFID event Albrecht premiered her final research on microchip induced tumors. Apparently RFID chips in bodies caused cancers to form around them, the technical term being foreign body tumor genesis. More information about this can be found spychips.com and antichip.com.
Video screening The Catalogue (UK 2005 | 5’30):
Techno Optimism
 The final speaker was Bart Schermer, secretary of the RFID platform, privacy specialist at ECP, and a privacy researcher at the University of Leiden. He immediately stated that he was a ‘techno optimist’ and a big fan of RFID. He tried to defuse the spychips threat as sketched by Katherine Albrecht, while saying he agreed with her on many points. He did this by asking us to go back in time and ask us if we would have stopped the internet’s development had we knew beforehand that it would also be used in morally reprehensible ways, for instance to spread child pornography. He said that no technology is inherently malevolent but that its uses may be. Although RFID is not inherently bad, he did see some possible threats: invisible data-collection, the possibilities for profiling, classifying, and tracking consumers, as well as ‘Minority Report’-style advertising. He said that none of this was likely to happen,
The final speaker was Bart Schermer, secretary of the RFID platform, privacy specialist at ECP, and a privacy researcher at the University of Leiden. He immediately stated that he was a ‘techno optimist’ and a big fan of RFID. He tried to defuse the spychips threat as sketched by Katherine Albrecht, while saying he agreed with her on many points. He did this by asking us to go back in time and ask us if we would have stopped the internet’s development had we knew beforehand that it would also be used in morally reprehensible ways, for instance to spread child pornography. He said that no technology is inherently malevolent but that its uses may be. Although RFID is not inherently bad, he did see some possible threats: invisible data-collection, the possibilities for profiling, classifying, and tracking consumers, as well as ‘Minority Report’-style advertising. He said that none of this was likely to happen,
because the primary goal of a company is to make money; not to blackmail customers nor follow them everywhere. RFID will be used to seduce its consumers and maximize their value. Companies are bound by law and it takes two to tango. Companies are not forcing you to use it.
To further the defuse the dangers of RFID he explained that some important Dutch laws are already in place:
- Surreptitious gathering of personal data is a violation of the data protection directive.
- The same applies to using personal data for other purposes than for which they have been gathered.
- Surreptiously monitoring and following people is a criminal offense.
- Targeted advertising without prior permission from consumers is a violation of the (European) data protection directive.
Bart Schemer then quoted Francis Bacon: ‘Human knowledge and human power meet in one, for where the cause is not known, the effect cannot be produced’, meaning ‘information is power’.
If information is power, then (personal) data will be used to profile and classify consumers. According to Bart Schermer, privacy is thus a means to maintain ‘economic equality’ between companies and consumers. Consumers (should) have a say in the processing of their personal data. He dared to add “It is you who is in control of your personal data”.
However, Dutch citizens value security higher than privacy. Over 70% of the Dutch citizens is in favor of using RFID-data for law enforcement purposes, and consumers seem to value convenience, price, and speed over privacy (even if they say differently sometimes). Therefore, the single biggest threat to privacy is YOU.
Bart sums up how he would like to change consumers:
- consumers should be (made) aware of the importance of privacy
- consumers must therefore be informed when, how and where RFID is used
- consumers must have the option to deactivate RFID at the point of sale (opt out)
- consumer organisations must inform their constituency about RFID on the basis of facts not on the basis of fear
The way forward for companies should be the following:
- use RFID in a responsible manner (privacy is good business sense)
- provide benefits not only to themselves, but also to consumers
- provide openness and transparency about the use of RFID
- provide a truly free choice for consumers
And for governments:
- create tools for the protection of privacy (PETs, RFID guardians, logo system)
- place the consumer in control
- monitor personal shifts in the balance of power, and correct where necessary (refrain from creating more investigative powers and coercive measures)
Finally, consumers should:
- take their responsibility in safeguarding their privacy and individual liberty
- be wary of buying into doomsday scenarios
- actively resist applications that violate consumer rights
To reiterate, Bart stated that no technology is inherently malevolent. It is easy to create a dystopian scenario (and way more fun) than creating a realistic one. However, we should not judge a technology solely on the basis of possible misuse or abuse.
Discussion
Katherine Albrecht responded to Bart Schermer by saying that the privacy directive is limited to Europe. And even when such a legal system is in place it is difficult to find violations. It is than even more difficult to find out what has been done with the data. How can you prove something when the data is privately owned and can be deleted with a simple click? She stated that Schermer has put too much trust in the law.
Schermer responded by saying that database law is from the 1970’s, and that so far it has little to say about whether a tag in your jacket should be considered personal data. The only solution is a critical consumer that can create a backlash against companies. Information, he says, is the most important currency in information society.
Asked whether technologies can be inherently good or bad, Albrecht stated that something like RFID can invite malevolence. When looking to history, we can see for example that Hitler could coordinate the execution of so many people precisely because demographics were recorded through IBM’s Hollerith punch card technology – this made it easy to quickly identify and localize Jewish communities and others.
Albrecht says that history tells us what we don’t want to know, which is that governments with too much power kill people. She argues that in the past century, national governments have produced more casualties than any other cause. Bart Schermer responds that there is difference between a technical system in place on the one hand and the rise of a dictator on the other. If the source of the problem is evil governments then we should look to prevent them from coming to power. Katherine states that the risks of RFID outweigh the benefits, and reminds us that Hitler was democratically chosen as well.
Summing up, the moderator makes a call for value sensitive design systems. Engberg adds to this, saying that so far, those paying the bills are choosing the wrong infrastructures for using RFID. Creating data does not ensure the creation of data regulation – that needs extra work. Albrecht notes that it only takes the stroke of a pen to change policy, and a button to avoid it. She says no privacy law will be enough, and instead pushes for a guerrilla attitude. Ultimately, she say, she is against the deployment of RFID. Period. At this point she makes an emotional appeal, saying that we are in a battle for our lives and those of future generations.
The discussion shifted to the terms of debate about privacy. At present there is a false dichotomy: privacy versus security. The real debate however, accoriding to Katherine, should be about freedom versus control. In the current debate, policy-makers can point out that privacy is for those who have something to hide. When she points out that privacy is not an end but a means to achieve freedom of speech, economic equality and other democratic goals, the other participants cannot help but agree.
The videos of all presentations will be available here soon.
Workshops
 On Saturday two workshops on RFID were held. One was on the social uses of RFID and the other about the ‘future histories of RFID’. In the former, led by Klaas Kuitenbrouwer, a group of people went into town to take pictures of everyday objects which could be socially enhanced by RFID. They came up with an augmented chess board, with which chess pieces could be tagged and games could be played with the help of friends located elsewhere. Another project talked about tags in stickers, through which friends and strangers could leave behind (URLs for) movies for one another. Yet another project was about leaving secret messages on bench, and this kept up a common theme of ‘dislocating’ and ‘relocating’ social interaction in different places at different times.
On Saturday two workshops on RFID were held. One was on the social uses of RFID and the other about the ‘future histories of RFID’. In the former, led by Klaas Kuitenbrouwer, a group of people went into town to take pictures of everyday objects which could be socially enhanced by RFID. They came up with an augmented chess board, with which chess pieces could be tagged and games could be played with the help of friends located elsewhere. Another project talked about tags in stickers, through which friends and strangers could leave behind (URLs for) movies for one another. Yet another project was about leaving secret messages on bench, and this kept up a common theme of ‘dislocating’ and ‘relocating’ social interaction in different places at different times.
 The second workshop, led by Richard Rogers and the Digital Methods Initiative, investigated information politics on RFID. The full report can be found at the Digital Method Initiative’s project page on Future Histories of RFID and in Timo Arnall’s excellent blog post. The research includes The Substantive Composition of RFID According to Folksonomy and the Web, Wikipedia Anonymous Authorship Cartogram: The RFID Entry, Drama in Search Space: RFID and Arphid Queries Over Time, RFID Imagery: ‘Wet’ and ‘Dry’ Associations Compared, and Issue Packaging on the Web: Style Sheets for RFID Sites by Site Type. Timo Arnall wrote a blogpost about the Future Histories of RFID workshop.
The second workshop, led by Richard Rogers and the Digital Methods Initiative, investigated information politics on RFID. The full report can be found at the Digital Method Initiative’s project page on Future Histories of RFID and in Timo Arnall’s excellent blog post. The research includes The Substantive Composition of RFID According to Folksonomy and the Web, Wikipedia Anonymous Authorship Cartogram: The RFID Entry, Drama in Search Space: RFID and Arphid Queries Over Time, RFID Imagery: ‘Wet’ and ‘Dry’ Associations Compared, and Issue Packaging on the Web: Style Sheets for RFID Sites by Site Type. Timo Arnall wrote a blogpost about the Future Histories of RFID workshop.
All pictures were made by Anne Helmond.
For another conference summary, see Twan Eikelenboom’s great post at Virtueel Platform.