Tribler: Who’s downloading?
Researchers of the Technical University in Delft (Netherlands) have released Tribler 6.3. Under the leadership of Johan Pouwelse a researching team works now for about 9 years on Tribler, an opensource p2p-client which makes use of the bittorentprotocol. In other words, Tribler is a downloading program which works the same way Bittorent does. So Tribler on it’s own is not new. What is new is the 6.3 update which makes it possible to anonymously download data from the Bittorent networks. Until now Bittorent users are easily traceable, because their IP-adresses are not masked. The developers of Tribler suggests that the implementation of parts of the anonymisation protocol Tor in combination with it’s bittorent implementation makes it possible to anonymously download data.
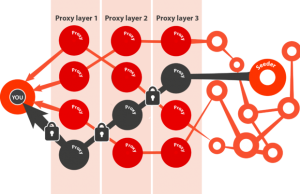
This movie will help you understand how the Tor network works
The anonymisation protocol of Tribler 6.3 makes use of multiple stations, which are known as proxies. A BitTorrent downloader, also known as a “leecher” makes contact with the first proxy which make sure that all the data will be locked and send to another proxy. The data will be locked over and over again after a link with the second and third proxy, whereupon the contact with the source (‘seeder’) will be made. According to the Tribler makers, the use of three proxy layers and multiple encryption layers makes it almost impossible to monitor the data traffic from the leechers. This makes the downloader invisible.
Tribler’s encrypted Tor routing
De ‘seeder’ is in this implementation in the new version of Tribler still visible. Pouwelse says that his team is working on a softwarecode which makes it also possible to hide the ‘seeder’. In order to accomplish this, an ‘end-to-end’ encryption layer has to be add to the torrentprotocol. In this case both the uploaders and the downloader will be ‘invisible’.
If Tribler succeeds in anonymizing the whole Bittorent-chain, the fight against illegal downloading will be more difficult. It will be harder for the regulators (agencies like Brein) and copyright holders to monitor or counter the spread of possible illegal content.
In an age where our privacy is becoming less, mostly due to social media sites like Facebook, Twitter and Instagram, I think it’s a good thing that more and more people find ways to enhance our anonymity on the Internet. This clears the path for, what I think, is the ideal situation on the Internet: the hi-tech gift economy. This concept was first mentioned by Richard Barbrook, who claims that on the Internet you need to have the possibility to freely share information with others (Barbrook). The Net (originally being invented for the U.S. military) was constructed around the gift economy. From its earliest days, the free exchange of information has therefore been firmly embedded within the technologies and social mores of cyberspace (Giese 130). For most of its users, the Net is somewhere to work, play, love, learn and discuss with other people. Unrestricted by physical distance, they collaborate with each other without the direct mediation of money or politics. Unconcerned about copyright, they give and receive information without thought of payment. On the Net, enforcing copyright payments represents the imposition of scarcity on a technical system designed to maximise the dissemination of information (Barbrook). The protection of intellectual property stops all users having access to every source of knowledge.
Organizations such as Brein, but also vigorous actions from governments, scare people to share data on the Internet. In the last few years some excessive fines were given for either uploading and downloading data. This is, in my opinion, a ridiculous situation and contradictory to the Internet as an social structure to encourage open cooperation among its participants.
With it’s new update, Tribler ensures that the ideal of a hi-tech gift community becomes more and more a reality. Both the downloaders as the uploaders will be masked, which means that they can’t be traced by either organizations like Brein or the government. In this case a lot more people will contribute sharing data on the internet. This will increase the collaboration between people and expand collective knowledge. Or as Lang points out: “Within the hi-tech gift economy, people successfully work together through “… an open social process involving evaluation, comparison and collaboration” (Lang 3).
References
Barbrook, Richard. “The Hi-Tech Gift Economy.” First Monday 3.12 (1998) 15 may 2013.
http://firstmonday.org/ojs/index.php/fm/article/view/631/552Levine
Giese, Mark. “From ARPAnet to the Internet: a cultural clash and its implications in framing the debate on the information superhighway.” Communications and Cyberspace: social interaction in an electronic environment. Eds. Lance Strate, Ron Jacobson and Stephanie B. Gibson. Cresskill, N. J.: Hampton Press, 1996. 126-132.
Lang, Bernhard. “Free Software For All: freeware and the issue of intellectual property”. Le Monde Diplomatique. (1998)