MIN(D)ING Your Data
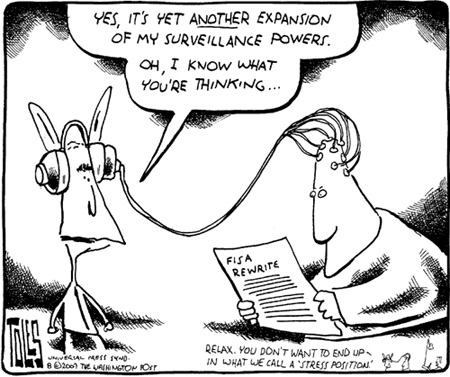
Last week, ‘surveillance and control’ was the theme the Masters of Media-students were debating about. Theorists as Michel Foucault, Deleuze, Galloway and Thacker and Chun passed the revue. With the articles of the last three theorist there was some pessimism going on during the discussions.
In their article ‘Protocol, Control and Networks’, Galloway and Thacker write about the network discourse that can be seen as a way to understand political control in society ’It is a totalizing control apparatus that guides both the technical and political formation of computer networks, biological systems and other media.’ Needless to say, most of our activities nowadays depend and are ruled by the distributed network. The individual is free in disseminating information, do business and spends a fairly big part of free time while surfing the net while leaving virtual traces. These online practices can be experienced as freedom in a positive way but Galloway and Thacker apparently have chosen the pessimistic point of view as they state: ‘this distributed character in no way implies a freedom from control’. Derived from the notions of the ‘dividual’ of Deleuze, all data on the web is subject to collection and thus we are. In the article, the two theorists are debunking the myth that the Internet is a celebration of freedom by focusing on the dangers as well. Wendy Chun on the other hand, is mediating between the, what she calls, ‘extramedial representations’ by which she means the utopian/dystopian notions and ‘research’ approaches about the freedom and dangers inherent in protocol and indispensable for the very existence of the Internet. Chun’s research is focused on the actual operations and operation failures of the Internet as seen as a global surveillance machine. Chun isn’t downplaying the analyses of Deleuze used by Galloway and Thacker; ‘This is not to say that Deleuze’s analysis is not correct but rather that it –like so many analyses of technology- unintentionally fulfills the aims of control by imaginatively ascribing to control power that it does not yet have and by erasing it’s failures.’ (p.9)
By analyzing the status quo of the Internet, by many imagined as a ‘global’ surveillance machine, Chun investigates the networked media and states that the Internet can’t exist without accepting the vulnerabilities users experience ‘Importantly, without this incessant and seemingly disempowering exchange of information, there would be no user interactions, no Internet. The problem is not with the control protocols that drive the Internet –which themselves assume the network’s fallibility- but rather with the ways protocols are simultaneously hidden and amplified.’
As previously mentioned, during the workgroup discussions of these different perspectives described above, I felt the dystopian notions about analyzing online personal data prevailed. For instance, Facebook users are subject to marketers profiling practices which for many students was felt as an abuse of their online traces and digital identity. The online personal content and conversations is confiscated by voluntarily agreeing with the terms and conditions of the social media platform. Although many users are aware of this fact, they agree, often without actually studying the terms and conditions. As the discussion went on, I felt the pessimists were overrepresented.
To keep things simple, imagine there are two parties in this debate. We have the pessimists and the optimists on the consumer surveillance theme. One party advocates the harvesting and analyzing of online personal information and to other party does not. In those parties you could place the consumer on the one side, and the owner or marketer using the scrapped data from social media networks for their advantage in the other. Where does this position the new media researcher in analyzing these systems of data retrieval and profiling? According to Richard Rogers who is the Director of the Digital Methods Initiative, there are concerns ‘how to make use of the copious amounts of data contained in online profiles, especially interests and tastes.’, which are in need to be answered by researchers like us, The Masters of Media-students who are likely to become the new media researchers. Rogers calls his approach ‘post-demographic’ which could be seen as ‘the study of the data in social networking platforms, and, in particular how profiling is, or may, be performed.’ Of particular interest here are the potential outcomes of building tools in top of profiling platforms,..’ (Rogers 2009) Post-demographic need to be understood as a different method than the traditional demographic research practices where, ‘race, ethnicity, age, income and educational level – or derivations thereof such as class..’ are subject of analyses. The ‘post-demographic’ research method instead is interested in ‘tastes, interests, favorites, groups, accepted invitations, installed apps and other information that comprises an online profile and its accompanying baggage.’(Rogers 2009: p 30)
My point is that the most pessimistic approaches of the consumer surveillance are actually counter to the very existence of this interesting field of study and position of the new media researcher. An approach which, correct me when I am wrong, maybe needs to be reconsidered by new media students who apparently have negative feelings about this research practice. As Rogers stresses, this method of doing research is very productive:
the platforms continually encourage more activity, inviting commentary on everything posted, and recommending to you more friends (who are friends of friends). With all the ties being made, and all the activity being logged, the opportunities for analysis, especially for social network researchers and profilers, appear to be boundless.‘(Rogers 2009)
To conclude, in 2008, a team consisted of UvA New Media analysts and technical developers worked on a project called ‘Vriendjespolitiek.net’. The project dealt with the way in which the characteristics of individuals could tell something about the individuals in combination with the characteristics of their friends/connections. The personal information is retrieved from the Dutch popular social media networking site Hyves. This project is a example of an post-demographic research method where ‘by providing appropriate visualizations we show both the demographics and the relations of a group of pals, and replicate the existing, arguably anti-participatory democratic, voting recommendation machines. Ultimately the goal is to raise awareness of one’s digital public self – one’s data body.’ (Well.com 1995) – to create conscience of simple yet powerful profiling techniques, and the tools of the surveillance and control society.’ So by doing research and actually utilizing ways to give the public insight in someone’s online appearance, there is a way to both use profiling techniques and let the users benefit from the transparency of the tools of surveillance by which the new media researcher, I think, is positioned in a somehow neutral position.
References:
– Rogers, R. (2009) “Post-Demographic Machines”. In Annet Dekker and Annette Wolfsberger (eds.), Walled Garden. Amsterdam: Virtueel Platform, 29-39.
– Chun, Wendy. (2006) ‘Control and Freedom. Power and Paranoia in the Age of Fiber
Optics’. Cambridge, MA: The MIT Press.
– Galloway, Alexander & Eugene Thacker. (2004) ‘Protocol, Control, and Networks’. Grey Room, Inc. and Massachusetts Institute of Technology
– Vriendjespolitiek.net. (2010), ‘vriendjespolitiek_paper.pdf’, retrieved at september 25, 2010.