Thou shall not lie (on your online profile)
(Untrustworthy) Online Identities in Web 2.0
The example of Facebook
As new media history is being written at present time, the discourse keeps revolving around the notion of online identity and “personal privacy” issues that are connected to the usage of social networking sites. It is a highly debated issue whether the representation of one’s self in a virtual, online community is a reliable source of information and what kind of danger derives from unreliable, anonymous online identities.
At first, the notion of online identity refers to the social identity that is constructed by an internet user and depicted as a “user profile” in virtual communities. It can involve a visual representation of the user (profile picture), a detailed description of the user’s background and it can be anonymous (i.e. nickname/pseudonym instead of real name). Undoubtedly, those public displays of one’s self cannot be always trustworthy sources of information. In other words, online identities in social networks can be unreliable. Naturally, the risk that is involved when dealing with “fake” online personas is a controversial issue and, as it usually occurs with such matters, there are two sides to the coin.
On the one hand, there are those who will argue that In the Web 2.0 era it is safe (enough) to socialize online. Take for example the case study of Facebook: Facebook has been designed to connect or reconnect individuals who have an offline bonding as well as an online presence. The social networking site of Facebook was designed to function as a medium to assist users to maintain relationships with acquaintances more than a medium for meeting new people (in comparison to the early days of social networks for dating purposes, eg Friendster). Moreover, the online identity of a user can be protected from “outsiders” as there is a dual confirmation between the users, before the actual connection of their individuated networks (i.e. the acceptance of “friendship”). Furthermore, there is a co-construction of the user’s online identity: i.e. my network is my credibility and my friendship links are vital proof for my online persona to other users. This could be compared to the case of the Danish social network Arto, for youngsters, where, as it has been proved, the connection, the network formed between the users co-constructed a reliable online identity, powerful enough to send all the possible intruders, possible fakesters away.
On the other hand, the risk of a personal life being unveiled is still high and online predators await to take advantage of one’s online identity. Again the case study of Facebook functions as the ideal example. There are two issues that are underlined as crucial regarding the privacy of the users. Firstly, there is an introvert issue that occurs amongst the users, regarding fake online identities. More specifically, a potential predator can befriend your online persona, and there is a chance that you can be “bullied” (the constant fear of parenthood) or persuaded to reveal private data. Then, there is an extrovert issue that depends on the privacy settings of the social network: it is true that a great shift has been noted recently, as users seem to experience the social management networking with personalized advertising and so on.
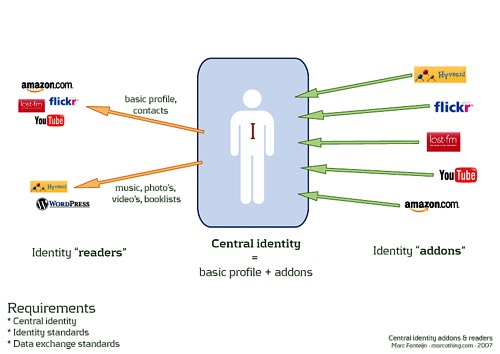
In the jungle of unreliable online identities, the fittest is not the one who survives; the actual survivor is the one who better controls the amount of information that is being distributed about him online. As Facebook functions today, members of a network can be instantaneously informed about an activity or a picture upload of a user, even without the user’s approval, due to the tagging system. Linking that to the matter of unreliable online identities, the user must be able to control not only the data that he shares with his network but also the data that other people upload about him. It is true that even the end of a user’s participation to a social networking site is not a radical solution anymore; instead the solution to this riddle is one of a double nature. In a more explicit way, the user must participate to control his online identity and protect it from other unreliable sources. Moreover, generally, a new model of online trust should be set forward: one should be responsible to create a real, trustworthy online identity on a personal level and all should be responsible to maintain a network with verified, controlled online identities. In this way, this new model of web trust would hopefully lead to a safer social network, where jeopardised situat ions would be elimininated and SNS‘ would be a safe playground. An online ground, safe for the user to join or even to leave knowing consiously that he will not be exploited after his depart.
Concluding, the paradox that occurs with online identities, reliability and control is a source of many questions that are yet to be answered; such as: is it possible for an online persona to be deleted, to disappear completely? Can one have the ultimate control over his online identity? Is it safe to trust other users, even acquaintances on a social network? Can a network ever consist of individuals with realistic online identities? And also, in user generated networks, such as Facebook, who is actually in control?
Works cited:
Albrechtslund, A. (2008). Online Social Networking as Participatory Surveillance.
First Monday, Volume 13, Number 3 – 3 March 2008
http://www.uic.edu/htbin/cgiwrap/bin/ojs/index.php/fm/article/viewArticle/2142/1949, last accessed on 26/09/2010
boyd, d. m., & Ellison, N. B. (2007). Social network sites: Definition, history, and scholarship. Journal of Computer-Mediated Communication, 13(1), article 11. http://jcmc.indiana.edu/vol13/issue1/boyd.ellison.html, last accessed on 26/09/2010
Donath, J. (1999). Identity and Deception in the Virtual Community [Electronic version]. In P. Kollock, & M. A. Smith (Eds.), Communities in Cyberspace (pp. 29-59). New York: Routledge.
JenQuin ( anonymous user) ( 2010),[Electronic version], http://networkconference.netstudies.org/2010/04/perceptions-of-identity-in-social-networking-controlling-your-online-presence/, last accessed on 26/09/2010
Larsen M.S. (2006), Understanding Social Networking: On Young People’s
Construction and Co-construction of Identity Online[Electronic version], http://www.ell.aau.dk/fileadmin/user_upload/documents/staff/Malene_Larsen_-_Documents/Paper_Malene_Charlotte_Larsen_REVISED_version_Sep07.pdf, last accessed on 26/09/2010