Book Review Hackers: Heroes of the Computer Revolution
O’Reilly published this year a new updated edition of the book Hackers: Heroes of the Digital Revolution from Stevy Levin. The book tells the history of a subculture that arose in the late fifties. The book starts in Building 26 with a boy wandering down the corridors in the middle of the night. The boy is Peter Samson, who will become one of the first generation hackers at Massachusetts Institute of Technology (MIT). Peter Samson is one of the many hackers mentioned in the book; the most important of them (the so-called Wizards) along with several machines are described in the preface of the book. Small, sometimes funny, descriptions accompany the names. John Draper, for example, is ‘the notorous “Capitain Crunch” who fearlessly explored phone systems, was jailed and later hacked microcomputers. Cigarettes made him violent” (xii) Even though Levy covers a lot of ground in 477 pages, it still is a remarkably coherent story. Levy talks about young hackers and their obsessive passion for the machine, about long nights spent trying to tame their mechanical beasts.
In his attempts to explore what hackers actually are, Levy defines the so-called Hacker Ethic, which reads as follows:
- All information should be free
- Mistrust Authority – promote Decentralization
- Hackers should be judged by their hacking (a meritocratic society)
- You can create art and beauty on a computer
- Computers can change your life for the better
As amazing as this ethic sounds, the remainder of the book describes how much of its power has unfortunately eroded over time. In the beginning of the ‘Computer Age’, almost no one had access to computers. Computers were only used by governments, big companies and institutions. Computers were huge, filthily expensive and needed the constant attention of a group of engineers. Only a small group of ‘experts’ were allowed to touch the machine, the computer was to vulnerable to be touched by others. Levy calls the former group the Priesthood, ‘and those privileged enough to submit data to those most holy priests were the official acolytes’ (Levy, 2010:5). In that time, some fanatic members of the Tech Model Railroad Club, at MIT had access to an IBM machine. Access was limited and heavily regulated, but in those day you couldn’t be picky. When a new computer called TX-0 entered MIT, the TMRC boys were becoming addicted to the machines. Because computeres were so expensive that it would be a waste to not use them 24 hours a day, the TMRC boys would hang around wating for an opening to occur. These boys would become the first generation of hackers. They would hack as long as they could and create new tools for the computer.
The market for the computers they used was extremely small so it was easy and quite natural to share your code and smart inventions. When the computer market opened up in the seventies, it became hard to uphold the Hacker Ethic. Second generation hackers didn’t seem have a problem with asking a price for their software. Stevy Levy focuses in this case especially on Bill Gates. Gates had created a program for the Altair, one of the first microcomputers, and was outraged when people started copying his program. He wrote a letter to the offenders entitled “Open Letter to Hobbyists”. In this letter he argues for proprietary software, how else could a programmer live?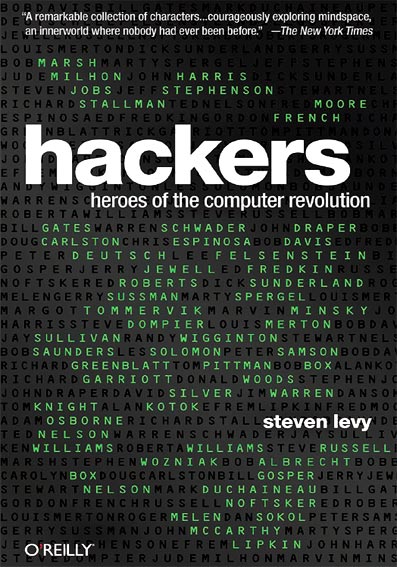
And so starts the decline of the Hacker Ethic. Hackers started companies and free information became encrypted. Capitalism overrules Freedom. In the last chapter Richard Stallman is called ‘the last of the true hackers’. Stallman is devoted to Hacker Ethic and he sabotaged the commercially evil Symbolics to stay true to his belief. Even now, he is still one of most important advocate of the Hacker Ethic. In the second afterword (the one from 2010) Levy revisits some hackers including Stallman. Levy states that Stallman ‘provided the intellectual framework that led to the open source movement’ (Levy, 2010:472). The book explains the widespread belief amongst hackers in the ‘Right Thing.’ Problems can be solved in multiple ways but in the world of coding there is always one solution which outshines all the others. This mastery of solutions is the Right Thing to do. Stallman is very persistent in doing the Right Thing, though not even his standards are what they used to be.
I have just given a short summary of the book and am painfully aware that it does not do justice to the book. The paragraphs above are just a small part of the complete story. The book is about the TX-0, computer languages, pranks, phone phreaking, games, artificial intelligence, logic, capitalism, bumming, 30 hour day cycles, intelligence, encryption, the rise of the personal computer, betrayal, political action, communities, success, failure, ethics and above all passion. The book celebrates the work of the hackers. Instead of describing them as smelly, autistic boys Levy transcends this stereotypical image. These hackers may be socially awkward (there are almost no women mentioned in the book) and no athletes, but they are ninjas in their own field. It just so happens that some of them don’t wash themselves regularly (like Greenblatt) but that is not what defines them.
It is clear that the early ideals of the hackers were unable to outmaneuver the outside world. In a way it has been a sad, yet also very inspiring story.. Code is not something that should be guarded, that should be hidden behind a flashy interface. When well executed, code is art all by itself. Code can be elegant, funny and sometimes obnoxious. I have the feeling that even though code is everywhere in our society, we don’t know anything about it. The hackers made tools to make tools. The pioneering microcomputer Altair was a kit which hobbyists had to assemble themselves. Nowadays we go to a shop to buy a shiny new laptop with a closed system. We pay attention only to the surface and forget that what lies beneath it, is a deep, rich territory just asking to be explored. It is like swimming in the sea and ignoring the fact that below your body is a breathtaking ecology. So, maybe it is time to get some goggles, or, if you feel like taking a risk, diving equipment. Let’s start exploring and experimenting. Let’s revive that passion of the early hacker. Because after reading this book you will know for certain that not only does culture change technology, but that technology also changes culture.
–
Levy, Steven (2010). Heroes: heroes of the computer revolution. O’ Reilly Media. ISBN: 978-1-4493-8839-3