Smart Home Technologies and the Transformation Of Domestic Space
Since Gordon Moore’s prophetic law in 1965, in which he claimed that microchips would develop so that the speed would double while size would decrease every year, has allowed for the evolution of ubiquitous computing and its introduction into the home (Mollock 2006). As technology becomes smaller, we see the addition of “smart” technologies in every facet of our lives. As Amazon’s Alexa is set to be in almost 50% of U.S. homes within the next two years, we are left questioning how these technologies are transforming our homes. How did these technologies come to prevalence, and do they constitute an advancement in the way we treat our domestic space, or is their extensive reach into our homes changing long established dynamics within the private sphere? Our aim with this project was to stage a critical intervention into the discourse surrounding smart homes by elaborating on current debates, and also offering our own critical frameworks based on a synthesis of our research.
While our work does not only focus on virtual assistants, we use Amazon’s Alexa software as a concrete example of “smart home technology” to situate our discussion within current debates around ubiquitous computing, security concerns, and gender and technology.
Ubiquitous Computing and “The Internet of Things”
In 1991, Mark Weiser coined the term “ubiquitous computing” which “describes a future world where invisible computers will be embedded in everyday objects to enable everyday activities” (Ebad 2004). This can in turn create a network within the home so we could live in a “calm” environment, where smart devices would “blend into the world and require little technical knowledge on the part of their users, and they “should be as simple to use as calculators, telephones or toasters” (Mattern 2004).
Eight years later, “The Internet of Things” coined in 1999 by Kevin Ashton, put forth the idea that a household of smart devices can create a network to collect, store and exchange data (Ashton 1999). It began with the most voluntary incidence of ubiquitous technology: The introduction of security cameras in the domestic space. Many rely on security cameras as their own personal method of surveillance in and around the home. This has now evolved into technologies such as Alexa Home Kit, which “enables keyless entry, guest access, and in-home delivery”, all monitored by a security camera, so that you can allow Amazon deliveries to be delivered inside your front door if you’re not at home on time for your delivery.
This raises the security concern of losing complete control of our own front door to Amazon. One might give a key to a trusted neighbour, but it is inconceivable to give a stranger access to your home. Consumers are happy to allow Amazon to enter their front door because it allows homeowners to be elsewhere while purchases arrive, rather than having to wait for a delivery that will come within a 6 hour window, it prevents wasted time waiting. The issue of not having enough free time comes from overworking and the unrealistic expectations we place onto ourselves with regards to filling our time. This is a problem created through neoliberal agendas and the atomisation of individuals. As we all become “human capital” as Read terms it, ‘Any activity that increases the capacity to earn income, to achieve satisfaction, […], is an investment in human capital’ , thus more free time means more time to invest in our “human capital” (Read 2009). However, is the issue it solves worth surrendering total control our our homes through the introduction of more computing?
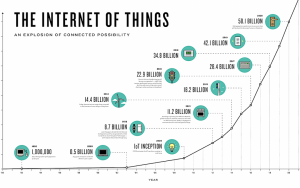
The exponential rise of the internet of things. Source: Medium
These ideas have since transformed into “pervasive computing” with negative connotations: the idea that digitized objects are so omni-present that they are extending into otherwise untouched domains, such as in the home. Creating a network of data flow, especially in the home through devices such as Amazon’s Alexa, is “bound to power and to its distribution and augmentation”: technology must be programmed, designed and distributed via corporations and advertising, which often leads to data collection and surveillance and the question (Rapoport 2012). There has been much study on surveillance technologies and self-surveillance, and how “the degree of ‘relative autonomy’ ” and the democratic possibilities in (global) civil society of using new technologies for liberation can be overstated and represented too optimistically” (Gill 1995).
Taking the home as a private space and how it’s being affected by smart devices, we must look at what constitutes a “private space”. The idea is that the domestic setting, the home, is a place with guaranteed “personal autonomy, privacy, and retreat” (Rapaport 2012). The home was, until the Internet of Things, a place where work was distributed between family members. However, with the addition of smart devices, much of the division of labor has fallen onto technology. This dependence on technology allows for corporations to gather even more data on users – and generally without users knowing the extent of the data collected, and “without effective data protection measures, the technology of ubiquitous computing could be used to create a surveillance infrastructure that would render ineffective many existing laws and privacy protection mechanisms” (Mattern 2004).
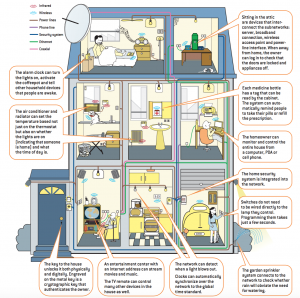
The Internet of Things. Source: Scientific American, 2004. Author(s): Neil Gershenfeld, Raffi Krikorian and Danny Cohen
Amazon’s integration to a variety of aspects in the home constitutes as transforming private space, whereby roles are distributed between technologies as opposed to human interaction, which, according to Mattern, brings about a different world whereby technology will be “equipped with spontaneous network capabilities and will thus be able to communicate and cooperate with other smart objects and to access all sorts of Internet resources” (2004).
We are currently living in the Internet of Things, evident in the the creation of Amazon’s Echo and Alexa system, and many other companies creating objects that are compatible with Alexa. Now there are well over 50 different compatible smart home technologies that work with Alexa, everything from lights, to “smart vents”, and even a small device called the “Automatic” that connects to your car’s diagnostic port, and using Alexa you can ask where you last parked or how long you were driving for. Alexa being able to connect to smart devices throughout the home connecting a vast interconnected network of exchangeable data constitutes being “an invasion of a private sphere” which could affect established “home” dynamics, as well as raising security concerns: “without effective data protection measures, the technology of ubiquitous computing could be used to create a surveillance infrastructure that would render ineffective many existing laws and privacy protection mechanisms” (Mattern 2004)
Privacy and Security
Consumer interest in connected home products is on the rise and people want to use the technology, but privacy concerns do still persist. Users feel negatively about companies using their personal data to figure out, for example, when they are likely to be home. Users want systems that help secure their homes, but don’t steal their personal data. This means smart home providers will need to prioritize security and privacy to catalyze mass adoption of their products, but this won’t come without challenges. Even though there have been security threats before, right now the number of threats is relatively low. This is mostly because there are no standard operating systems, like the way we have Android or iOS for phones, for Internet of Things devices. This makes it more difficult for cyber criminals to execute large-scale attacks. Rolf H. Weber states in his research on the impact on the security and privacy of the involved stakeholders that “with the emergence of an Internet of Things, new regulatory approaches to ensure its privacy and security become necessary. In particular, attacks have to be intercepted, data authenticated, access controlled and the privacy of customers (natural and legal persons) guaranteed” (Weber 2010).
Security must thus be a fundamental quality developers take into account when developing their devices. Manufacturers must keep safety in mind in the beginning phases of designing a product and test their products for weak spots. Users can often not easily assess the impact of the safety and privacy risks of a product. Many manufacturers store the data they collect with their Internet of Things devices and most consumers are not aware of this. Many would rather have the assistance without the burden of understanding, the pros outweigh the cons. Even if some users are aware of the fact that their data is being collected and stored, many people have the attitude that they have nothing to hide, but do not consider critically the consequences that security breaches could have.
In their research on the features and challenges of security and privacy in the Internet of Things, Roman et al state that the protection of personal information is very important but that “there is another dimension of privacy that is especially relevant in the context of the Internet of Things: the existence of entities that profile and track users without their consent. Here, the benefits of a distributed Internet of Things might turn into nightmares when misused” (Roman et al 2013). It is necessary to continue working on awareness so that users can make an assessment of the possible risks before purchasing an Internet of Things device. As long as they are not aware of the risks, cyber criminals have power over them.
These glaring security flaws are what lead many to consider increasing the interconnectedness of home appliances for convenience to be “solutionist thinking” (Morozov 2013). This term, first used by Evgeny Morozov, with regards to technology, is defined by him as “sexy, monumental and narrow-minded solutions (ibid.) They are answers to problems that confront the issues from a flawed and superficial point of view. Smart homes as a solution to this issue do not address the real problem because “many problems are not suited to the solutionist tool-kit. It’s also that what many solutionists presume to be ‘problems’ in need of solving are not problems at all; a deeper investigation into the very nature of these ‘problems’ would reveal that the inefficiency, ambiguity, and opacity – whether in politics or everyday life – that the newly empowered geeks and solutionists are rallying against are not in any sense problematic”(ibid.). “Traditional security countermeasures cannot be directly applied to Internet of Things technologies due to the different standards and communication stacks involved. Moreover, the high number of interconnected devices causes scalability issues to arise; therefore a flexible infrastructure is needed able to deal with security threats in such a dynamic environment” (Sicaria et al 2014). While these technologies might offer new forms of privacy and safety in some ways, they can also be productive of a domestic space that is more vulnerable to more external threats and intrusions, both corporate and criminal.
If we don’t want the Internet of Things to become the Internet of Trouble, we need to emphasize the priority of digital safety when designing, producing and selling these products.
Gender and Expectation in the Smart Home
Another aspect of smart home discourse which into which we wanted to intervene relates to the role of gender and expectation in the smart home. Smart home technologies are often marketed as being gender-neutral and accessible to the whole family. While the language of the smart home ad is rooted in “convenience,” “efficiency,” the visual imaginary of the smart home is centered in representations of its usability for everyone in the family. For example, many Amazon Echo advertisements feature families gathered around around the device.

Source (clockwise): PCMag, YouTube, The Telegraph, The Daily Dot
However, as one early Echo advertisement demonstrates particularly well, the gendered dynamics that can emerge within the smart home can seem innocuous, especially when they are situated within the larger “for the family” framework of these advertisements. And they certainly look better to modern eyes when compared to, say, cringeworthy domestic technology advertisements from the 50s. But we contend that it is nonetheless important to analyze the discrepancies between the imaginaries of smart homes versus the dynamics shaped in practice by asking questions like: who exactly do these technologies benefit and how might they be both reorganizing gender and labor in the home and also generating new relationships of power and control?
Those optimistic about the potential of these innovations to reorganize and reimagine domestic labor point to the “technology dads” who they claim are “challenging traditional roles in the home by engaging in flexible child care and work arrangements” as a result of the afforded conveniences of technologies (Strengers 2015). And as one scholar argues, the smart home offers new forms of labor and leisure and for men in the home (Strengers and Nicholls 2018). These forms of labor mainly revolve around the concept of what Strengers and Nicholls call “pleasance,” or the aesthetic pleasures of the home, whether that be nice music, lowered lights, or other atmospheric considerations (2018). In other words, these are the more immaterial tasks and aesthetic considerations of the home that can also generate social capital—it is the kind of networked capacity that you would want to show off to your friends at a dinner party. It’s the kind of labor that can be summed up with, to quote a party host in another Echo ad, “Alexa, set the mood!”

Source: Mashtips
While such activities along with the troubleshooting and configuration that smart home technologies require are creating new modes of domestic participation, this new position of what I would call “systems manager” tends to be male-dominated. Men are usually responsible for introducing these technologies into the home and are the primary controllers (Bowles 2018).
What this imbalance in control of the smart home can result in is a somewhat ironic reinforcement of traditional divisions of labor when the controller is too occupied with troubleshooting or configuration of the smart home, leaving more routine tasks to the other members of the family (Strengers and Nicholls 78). Other members of the family can also be excluded from the new forms of aesthetic and immaterial labor simply because they are not familiar with how the technologies operate.
A much more troubling outcome of this imbalance of control is the weaponization of the smart home. As The New York Times reported in 2018, smart homes have become a new mechanism of domestic abuse. Over 30 women contributed horrifying stories of thermostats raised to uncomfortable temperatures, locked doors with changed codes, and consistent surveillance by abusers who were able to control and configure the homes remotely as a means of asserting control. Unfortunately, this is no localized phenomenon. The problem has become so widespread that University College London, in collaboration with domestic violence prevention organizations, created a resource list for those who have been victims of technology-affiliated abuse. While such instances might seem extreme, we believe it is illustrative of the fact that, as tempting as it might be to believe that the automation of certain tasks in the home somehow “liberates” women from traditional domestic expectations, such notions flatten the complex (and still existing) social and historical factors that created and perpetuate such dynamics. In ignoring these complexities, we do not erase them—we only absolve ourselves from the responsibility of critically examining and working to change them. Perhaps, then, we might also ask whether some technologies of “convenience” might also be tools of complacency.
In this vein, we propose an intervention in the discourse surrounding the smart home that takes a critical stance on the ways in which the smart home does not necessarily afford the same new forms of labor and leisure to all of its users. We not only need to look at the ways that power relations are configured and mediated between corporate actors and private consumers through these technologies, but their potential to reconfigure power dynamics within the household. Yes, the smart home is continuously adaptable and dynamic, creating an efficient and supposedly “frictionless” environment. But at the same time, it can also create a domestic space in which labor and power may be unequally balanced, hidden within the pretenses of convenience.
No “ideal” home, no singular future
With this project, we hope that we have offered some new critical angles through which to understand networked technologies in the home and the impacts that they might have on domestic space. However, one thing that we want to make clear is that there is no uniformly “ideal” home, smart or not. Dynamics within domestic spaces are complex systems, influenced by a whole host of factors existing within the space and outside of it. And while we do acknowledge that smart technologies can offer new forms of leisure, comfort, and convenience for a lot of people, our goal has been to ultimately push back on notions that smart home technologies are part of a somehow superior and inevitable future.
References
Ashton, Kevin. That “Internet of Things” Thing. https://www.rfidjournal.com/articles/view?4986
Bowles, Nellie. “Thermostats, Locks and Lights: Digital Tools of Domestic Abuse.” The New York Times, 23 July 2018.
Ebad, Ryhan. “Ubiquitous Computing: A Brief Review Of Impacts And Issues”. MAGNT Research Report, vol 2, no. 3, 2014, pp. 59-68., http://brisjast.com/wp-content/ uploads/2015/06/May-7-14.pdf.
Gill, Stephen. “The Global Panopticon? The Neoliberal State, Economic Life, and Democratic Surveillance.” Alternatives: Global, Local, Political, vol. 20, no. 1, 1995, pp. 1–49. JSTOR, JSTOR, www.jstor.org/stable/40644823.
Gram-Hanssen, Kirsten, et al. “Gender and Ethical Consumption of Energy in Smart Homes.” Journal of Consumer Ethics, vol. 1, no. 2, Oct. 2017, pp. 111–19.
“Moore’s Law And The Future Of Iot – Mybit – Medium”. Medium, 2018, https:// medium.com/mybit-dapp/moores-law-and-the-future-of-iot-d9ed7d725f0a.
Mattern, Friedemann. “Wireless Future: Ubiquitous Computing”. 2004, https:// pdfs.semanticscholar.org/d603/c93e130ec7824193f5d2fb7d200cc654408b.pdf.
Mollick, E. “Establishing Moore’s Law”. IEEE Annals Of The History Of Computing, vol 28, no. 3, 2006, pp. 62-75. Institute Of Electrical And Electronics Engineers (IEEE), doi:10.1109/mahc.2006.45.
Morozov, Evengy, “To Save Everything Click Here: The Folly of Technical Solutionism”, Public Affairs Publishing, 2013, pp. 1-16
Rapoport, Michele (Michal). “The Home Under Surveillance: A Tripartite Assemblage”. Surveillance & Society, vol 10, no. 3/4, 2012, pp. 320-333. Queen’s University Library, doi:10.24908/ss.v10i3/4.4280.
Read, Jason, “A Genealogy of Homo Economicus: Neoliberalism and the Production of Subjectivity”, In: Binkley, S, Capetillo-Ponce, J (eds.) A Foucault for the 21st Century: Governmentality, Biopolitics and Discipline in the New Millennium. Newcastle upon Tyne, Cambridge Scholars Publishing, 2009
Roman, Rodrigo, et al. “On the Features and Challenges of Security and Privacy in Distributed Internet of Things.” Computer Networks, Elsevier, 28 Mar. 2013, www.sciencedirect.com/science/article/pii/S1389128613000054.
Sicari, Sabrina, et al. “Security, Privacy and Trust in Internet of Things: The Road Ahead.” Computer Networks, Elsevier, 18 Nov. 2014, www.sciencedirect.com/ science/article/pii/S1389128614003971.
Strengers, Yolande. “There’s a Problem with ‘Smart Homes’: They Appear to Be Entirely Designed for Men.” Business Insider, 25 Nov. 2015, https://www.businessinsider.com.au/theres-a-problem-with-smart-homes-they-appear-to-be-entirely-designed-for-men-2015-11.
Strengers, Yolande, and Larissa Nicholls. “Aesthetic Pleasures and Gendered Tech-Work in the 21st-Century Smart Home.” Media International Australia, vol. 166, no. 1, Feb. 2018, pp. 70–80. Crossref, doi:10.1177/1329878X17737661.
Tanczer, Leonie, et al. Gender and IoT (G-IoT) Resource List. University College London, July 2018, https://www.ucl.ac.uk/steapp/research/projects/digital-policy-lab/g-iot-resource-list.
Weber, Rolf H. “Internet of Things – New Security and Privacy Challenges.” Computer Law & Security Review, Elsevier Advanced Technology, 26 Jan. 2010, www.sciencedirect.com/science/article/pii/S0267364909001939.