Prey – an open source anti theft solution for Mac, PCs & Phones [Review]
 Gadgets are expensive, and quite easy to steal. Mobile phones and laptops are easy targets for thieves because they fit in pockets and bags, and there is a high demand for them on the black market. Prey is a program that should help you feel more relaxed when using your brand new macbook pro in public. It lets you keep track of your phone[1] or laptop if it is lost or stolen. For the Masters of Media blog, I have tested the application Prey 0.5.3 on Mac Osx Lion10.7.1.
Gadgets are expensive, and quite easy to steal. Mobile phones and laptops are easy targets for thieves because they fit in pockets and bags, and there is a high demand for them on the black market. Prey is a program that should help you feel more relaxed when using your brand new macbook pro in public. It lets you keep track of your phone[1] or laptop if it is lost or stolen. For the Masters of Media blog, I have tested the application Prey 0.5.3 on Mac Osx Lion10.7.1.
Installation and memory usage
The installation is rather easy and requires you to create an account and to install a light application on your computer. Once installed, no icon or applications are visible making it very hard for a thief to realize he is being tracked or to uninstall it.
Prey will not slow down your computer as long as it is not activated: On Mac and Linux, the program doesn’t use any of your resources as long as your computer hasn’t been reported as missing. In windows however, it constantly uses 5 little Megs of ram in the background. This means that you don’t have to worry about the program running all the time in the background because it is actually not running unless you want it to.
How it works
Prey runs in the background of your notebook and wakes up at specific interval to connect to the Internet. If the computer isn’t connected to the Internet, Prey will attempt to find an open Wi-Fi connection to connect itself. Once connected to Internet, Prey checks whether the user has reported the laptop as missing or not. If the laptop has not been reported as missing, the program goes back to sleep and nothing happens.
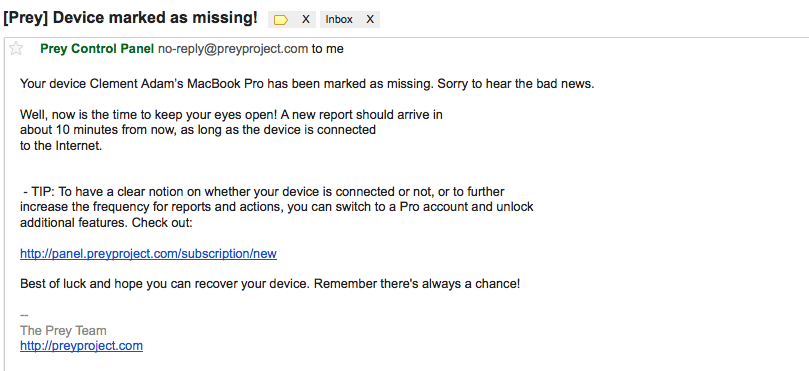
If the computer is really missing (or you’re just testing the application like me), the victim needs to access the Prey website with his account details from another computer and declare the object as “missing”.
The web based control panel
The control panel is a rather simple yet informative : hovering the mouse over the question marks provides more information on the possible actions that can be ordered using Prey. The web based control panel allows the users to configure what should appear in the report sent by Prey. Free users will receive a report every ten minutes whereas the PRO (paid) account users can request a report on demand (without waiting ten minutes).
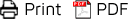
Key Features
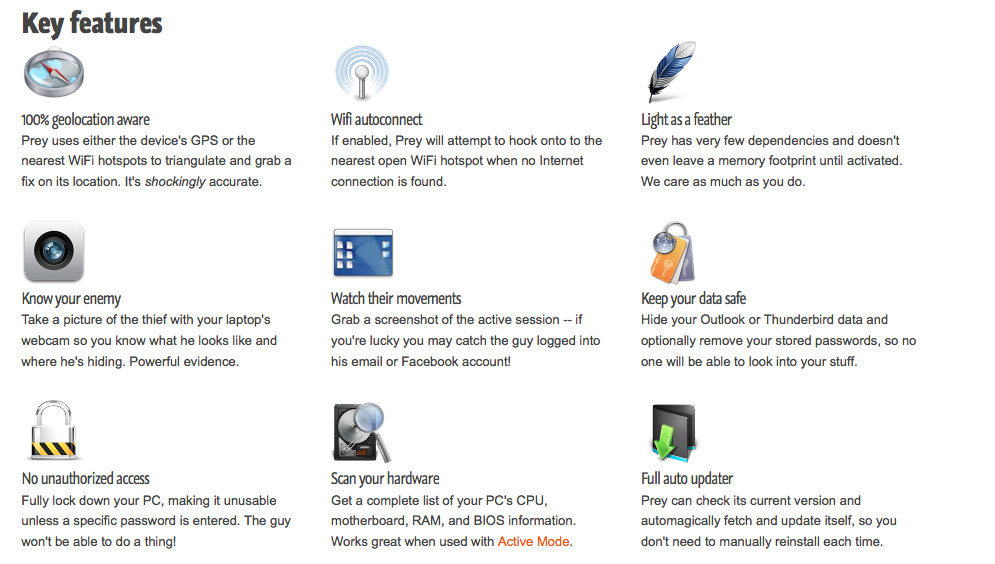
I have decided not to write about every feature of Prey because it basically does what their website says. A little word on the localization feature: Prey uses a device’s GPS or the nearest WiFi hotspots to triangulate a location. The location of the computer is thus shown on a map on the report. Clicking on the map will show the laptop’s location on google maps, with the complete address. Out of three tries, the program found my home address once and found my neighbors’ twice. This is actually pretty accurate!
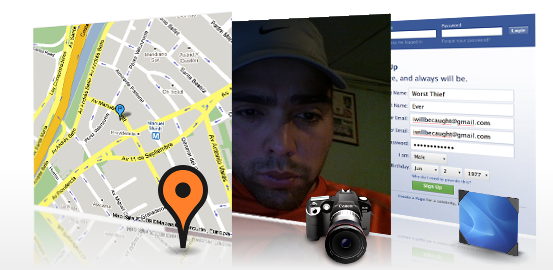
Another feature I particularly liked was the alert action – which allows you to send a message of your own creation to the thief.
Discussion
Overall Prey is an application that can come in very handy if one of your devices is missing. There are however concerns about the services (since it is a free application), people are afraid that the project will not be updated or that the customer service is bad. The PRO accounts are reassuring for us free users because it means that the company has a possibility to make money and to keep it running. Another debatable aspect is the way people react when they discover that their machine has been stolen. One could notify the police by giving them as much information as possible. One could send messages to the thief to kindly return the object. One could get a group of friends and give the thief a good lesson.. I let you decide how you would handle it.
Finally, Prey could also be used in malicious ways. Prey is the perfect program to spy on people since it runs in the background and does not show up in the application list or login items. For instance a jealous boyfriend could install this on his girlfriend’s computer to see what she is doing, where she is and who she’s with.
Pros & Cons
Pros
- Free
- Open source (so you can see that your information is not used for evil purposes)
- Lightweight
- Accurate
- Works on major operating systems
- Easy to operate
Cons
- 10 minute interval between reports (for free users)
- Re-installing the OS deletes it.
- The green light of the Mac webcam turns on when the picture is taken, which could alert a thief that he is being watched.
The verdict
Prey is the kind of program that you encounter when it’s already too late. Get it while you still can, it’s a definite must if you care about your laptops/phones.
[1] The Iphone and Ipad are not supported yet but fear not and have a look at Duohuai’s post if you have an Iphone!